“Google is the first imperialist power of the 21st Century” – Anonymous Comment.
Time is of the essence here. Therefore this is just a rough outline of an argument that I would love to see this fleshed out by researchers and/or an investigative body of the EU. It also likely has more than the usual amount of typos.
My hypothesis is that Google lobbying has crossed the rubicon and is now indistinguishable from the kind of hybrid war and information war conducted by hostile states, foreign intelligence services, and terror groups. Although Google doesn’t (yet) conduct kinetic operations, its activities seem to nicely fit all the other accepted tenets of hybrid war. Especially in the use of proxies (“little green men”) and information manipulation, disturbance, degradation and denial.
IMHO Google’s machinations in the debate over the proposed EU copyright directive are so far beyond the pale it’s an open question whether Google as now constituted is compatible with free and functioning democracies. To a lesser extent almost all Silicon Valley firms employ these same sort of lobbying techniques. Certainly these firms lend support to Google in these campaigns. They don’t say no anyway. Depending on your viewpoint there now exists a sort of “Sandhill Pact” or “Sandhill Axis” that is increasingly willing to undermine democratic processes through fakery and misinformation.
If you consider the Information Space as the 21st century theatre of war, Google is clearly the dominant power. They have more resources than all nations states put together. Although democracies can be attacked and destroyed through kinetic warfare they appear to be even more vulnerable to information warfare.
Is time to seriously consider actions by Google in the “information space” as threats to national security?
Hybrid Warfare
Hybrid warfare is a military strategy that employs political warfare and blends conventional warfare, irregular warfare and cyberwarfare with other influencing methods, such as fake news, diplomacy and foreign electoral intervention. By combining kinetic operations with subversive efforts, the aggressor intends to avoid attribution or retribution. –Wikipedia Contributors.
While on first brush this may seem rather strong to compare Google interventions in the democratic processes of sovereign nations as warfare. But this is largely because most people have a 19th century view of warfare as purely kinetic operations. In the last 50 years the information component of war has grown in importance. In the last 10 years it is arguably it the most important and effective component of modern warfare.
I’m confident both United States and Russian military thinkers would agree that nations on the periphery of the Russian federation have been yanked in out of the American sphere of influence largely via hybrid/information warfare. Kinetic operations were only used as a last resort. Think of simmering conflicts in Ukraine and Georgia. While ISIL has used stunning displays of violence to claim and hold territory, the group largely used this to further psychological campaigns and thus weaken opposing security forces. These forces “melted away” with little kinetic warfare. ISIL was able to expand its territory dramatically with a few thousand fighters. If you step back from the violence, ISIL has largely conducted an information war.
Kinetic operations are relatively unimportant in modern warfare, so even though Google lacks kinetic elements, the rest of it’s operations are strikingly similar to the techniques used by state actors and terrorist groups.
Remember that a group or nation does not need to gain territory or achieve a clear victory to benefit from hybrid war. Simply weakening “adjacent” nations or opponents may produce tangible benefits.
Use of Proxies
Proxies have long been used in warfare. Russian czars and the Cossacks. US and Hmong. Hybrid warfare importantly relies on the use of proxies not just for kinetic operations but also in information warfare. As noted in the wikipedia description of hybrid warfare “by combining kinetic operations with subversive efforts, the aggressor intends to avoid attribution or retribution.” The lack of attribution is key to Google’s strategy here in battle over the Copyright Directive. They don’t want to be punished by MEPs for seeming to have directly attacked them.
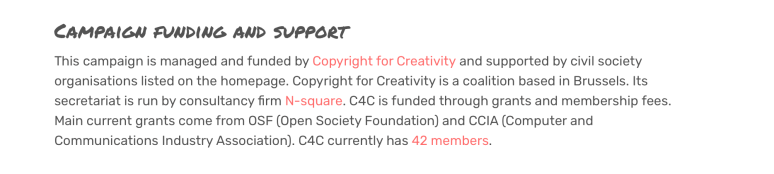 On a macro level the proxy here is pretty obvious. The SaveYourInternet.eu campaign is run by N-Square consulting. (Read the text carefully.)
On a macro level the proxy here is pretty obvious. The SaveYourInternet.eu campaign is run by N-Square consulting. (Read the text carefully.)
This firms biggest client is Google. Though many of the other listed clients receive Google funding as well. Most notably CDT.
 But on a micro level the campaign against Article 13 is much more disturbing. If you accept the premise the “real signal” or “information” the MEPs need for the vote is “what does the directive do” and “what do my constituents think” fake constituents providing manipulated or outright false information are doubly effective. If they are once or twice removed proxies Google can again escape retribution.
But on a micro level the campaign against Article 13 is much more disturbing. If you accept the premise the “real signal” or “information” the MEPs need for the vote is “what does the directive do” and “what do my constituents think” fake constituents providing manipulated or outright false information are doubly effective. If they are once or twice removed proxies Google can again escape retribution.
As supporters of the EU copyright directive began to push back and note Google opposition, a countering wave of misinformation was released. Here is a twitter account distributing highly misleading information.
 This does not seem to be true as Google did not lobby for upload filters. Or if they did, they simultaneously lobbied against the overall directive. Further the tweet that Joe highlights is old and taken out of context. And Joe knows this (see below). It’s a quote about Content ID (YouTube’s proprietary rights management system.) But since we are discussing proxies here, what’s more important is Joe is a Google proxy.
This does not seem to be true as Google did not lobby for upload filters. Or if they did, they simultaneously lobbied against the overall directive. Further the tweet that Joe highlights is old and taken out of context. And Joe knows this (see below). It’s a quote about Content ID (YouTube’s proprietary rights management system.) But since we are discussing proxies here, what’s more important is Joe is a Google proxy.

 Joe is executive director of EDRI. And EDRI is funded by Google.
Joe is executive director of EDRI. And EDRI is funded by Google.
https://www.theregister.co.uk/2015/04/29/google_doubles_eu_lobbying/
And EDRI is campaigning very hard against the EU copyright directive.
Proxies manipulating,disturbing and degrading information are all hallmarks of hybrid information war. That is exactly what this guy is doing.
Now one tweet is simply an anecdote. But this guy is a key figure and there are many similar tweets. I’m confident that one could easily build a convincing connectivity graph of tweets, retweets, followers and compare that to academics, lobbyists and NGOs fron the Google Transparency Project. Look at some of the organizations/individuals in reports below and see if they are weighing in on the copyright directive.
Featured Project Google Academics Inc. July 11, 2017 Read article
Blog Google Funds Dozens of Groups Fighting Sex Trafficking Bill September 27, 2017 Read article
Featured Project Google’s Academic Influence in Europe Read article
Blog US Congressional Privacy “Debate” Dominated by Google-funded Voices February 20, 2018
Blog Investigating Google’s European Revolving Door January 25, 2017 Read article
Featured Project Google’s European Revolving Door June 4, 2016 Read article
Weapons of Information Warfare
In a 1999 student paper a graduate student at Carnegie-Mellon University (Megan Burns) succinctly laid out the basic categories of weapons used in Information warfare. These were summarized from a broader work on information warfare by Martin Libicki(1995) It’s a succinct read that’s why I highlight it (hope ms. Burns got an A). The key five elements are:
Information Collection
Information Transport
Information Protection
Information Manipulation
Information Disturbance, Degradation and Denial.
In information warfare the side that is able to dominate in all these weapons categories is impossible to to defeat. At least without resorting to kinetic operations.
Information Collection
Google by the design has an extraordinary advantage over the EU Parliament. Its Android OS, Gmail, Website analytics and ad networks give it crucial information on virtually everyone on the planet. The EU government? Not so much.
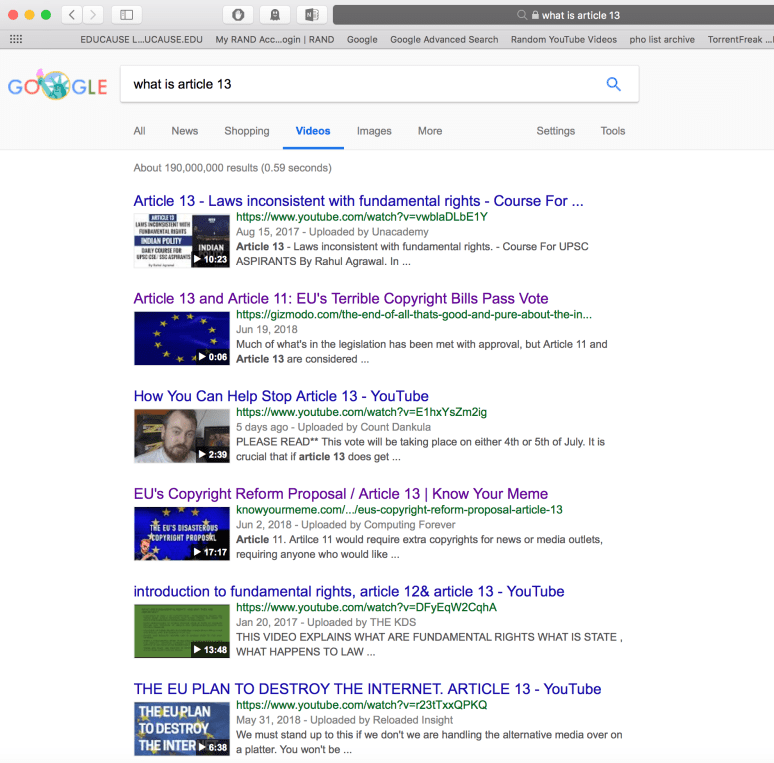
Information Transport
More than 90% of all web searches are conducted through Google’s search engine. Also the default mobile search in the Apple iOS is Google. Android is a wholly owned Google product. Most people click on the first few results. Google does not have to block information to suppress opponent information. They simply down rank links. Look at the screenshots below. These searches were conducted using private browser and VPN to minimize “browsing bubble” effect on search results.
“By scrambling its own messages and unscrambling those of the other side, each side performs the quintessential act of information warfare, protecting its own view of reality while degrading that of the other side.” -Martin Libicki
Information warfare is about distorting reality. To win in information warfare your reality must win out over opponents reality. Even actual positivist reality.
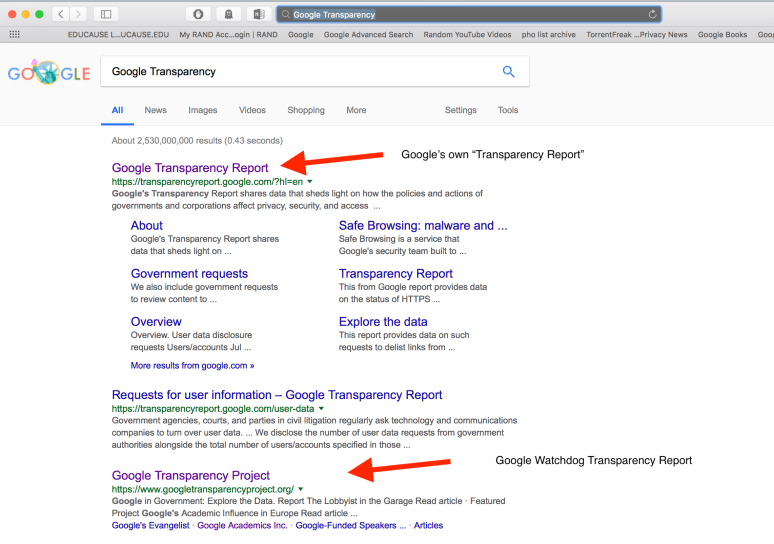
It’s not just enough to control the information flow. In information warfare a entity must protect information that the other side could use to damage your capabilities. In the case of Google they are expert at “Google washing” or obscuring damaging information. There is no better example of this than the Google’s own “transparency report” that confuses opponents searching for “Google Transparency Project.” Which one would your typical MEP staffer click on? By outranking adversary’s competing information, Google partially shields itself from damaging information. Remember Google controls the Information distribution channel. Essentially Google through the power of its search engine has the power to encrypt damaging information will decrypting and disseminating information that harms its opponents.
Information manipulation in the context of information warfare is the alteration of information with intent to distort the opponent’s picture of reality. This can be done using a number of technologies, including computer software for editing text, graphics, video, audio, and other information transport forms. Design of the manipulated data is usually done manually so those in command have control over what picture is being presented to the enemy, but the aforementioned technologies are commonly used to make the physical manipulation process faster once content has been decided. – Megan Burns
In this instance we see Google Proxy SaveYourInternet.eu conduct a three step process, that allows them enormous command and control over information directed at MEPs.
Step 1. Google proxy creates disinformation and images to share.
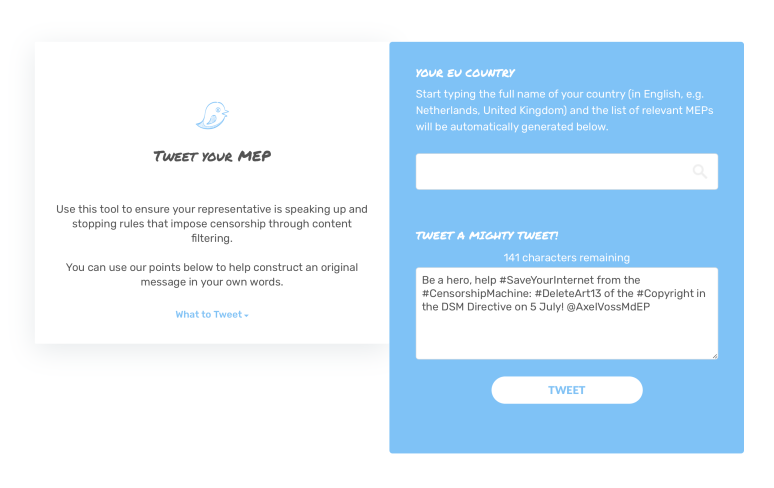
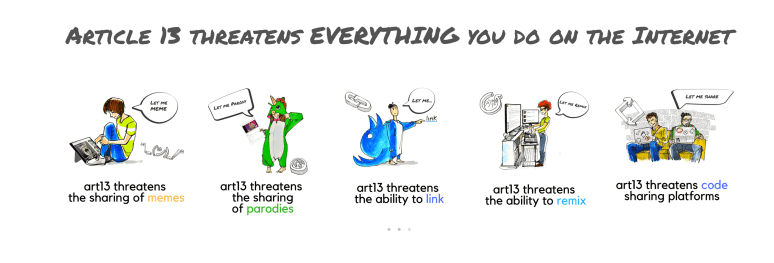 Step 2. Google proxy creates technological tools to distribute the misinformation.
Step 2. Google proxy creates technological tools to distribute the misinformation.
 Step 3. Some real constituents use these tools. But the tools were also used en masse by unknown(?) allied parties.
Step 3. Some real constituents use these tools. But the tools were also used en masse by unknown(?) allied parties.
Any particular country’s MEPs can be targeted by SaveYourInternet.eu. As images indicate Axel Voss was being automatically targeted when image was captured.
Information Disturbance, Degradation and Denial.
“Spoofing is a technique used to degrade the quality of the information being sent to the enemy. The enemy’s flow of information is disturbed by the introduction of a “spoof”, or fake message, into that flow. The technique works because it allows you to provide “false information to the targeted competitor’s collection systems to induce this organization to make bad decisions based upon this faulty information,” Cramer 1996
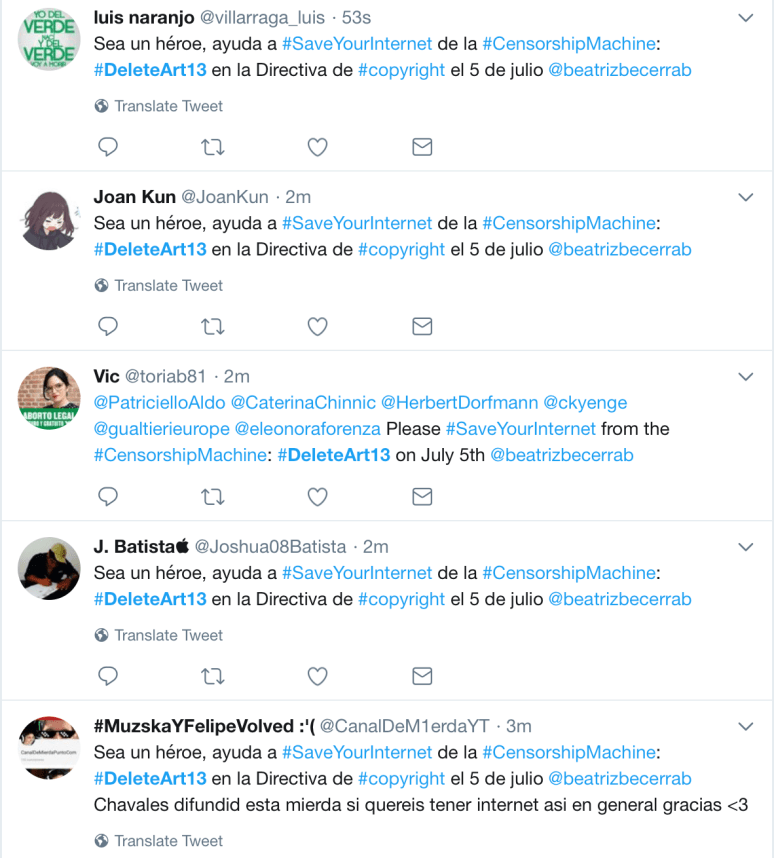
Thousands of tweets against copyright directive have been sent to MEPs from fake twitter accounts. “The enemy’s flow of information is disturbed by the introduction of a ‘spoof’, or fake message, into that flow.” Zoom out and there is an grander fake message: thousands of constituents are outraged by the copyright directive.
Finally as evidenced by the automated tweets, SaveYourInternet.com targeted specific MEPs at different times. “provide false information to the targeted competitor’s collection systems to induce this organization to make bad decisions based upon this faulty information.” See targeted robo tweets below.
Hundreds of automated tweets an hour directed at MEP Beatriz Becerra. Quite surprising since it’s the wee hours of the morning and the frequency of tweets seems to be increasing!?
So you got it? A Google funded webpage using automated tools to misinform and mislead a member of EU parliament, using what often appears to be fake twitter accounts. What do we call this?
“Another way to disturb the information being received by one’s opponent is to introduce noise into the frequency they are using. Background noise makes it difficult for the enemy to separate the actual message from the noise.” -Burns 1999
Again see above. The volume of automated tweets makes it impossible for MEPs to “hear” information that Google does not want them to hear. Say voices of artists and other creators that might be in favor of the copyright reforms.
“Finally, overloading is technique used to deny information to the enemy in both military and civilian settings. By sending a volume of data to the enemy’s communication system that is too large for it to handle, one causes a crash or severe degradation of the system’s ability to deliver information. The system is so busy dealing with the overload, it is unable to deliver the essential information to those who need it.”
By flooding MEPs with thousands of Spam messages, phone calls and emails, the fake information overwhelms all other information that might be useful to MEPs as they consider this bill.
Conclusion
The EU should investigate Google as their actions and those of their apparent proxies bear the hallmarks of hybrid information warfare. The future of democracy in the EU is at stake. These techniques could easily (and probably have been) replicated by state actors interested in undermining EU on other issues.


You must be logged in to post a comment.