Editor note: This has been translated from original german text here. Of particular significance Mr. Rieck suggests that the websites associated with the political hack, OpenMedia, New/Mode, SaveYourInternet EU and (their cloned sub-websites appear to violating e-Commerce directive proper disclosures (ownership) and New/Mode violating GDPR on user data.
Anatomy of a Policy Hack Part 2 – The Organization of Hacks
As mentioned in a previous article, saveyourinternet.eu’s campaign was primarily responsible for the flooding of MEPs’ mailboxes with ready-made e-mails their Twitter accounts with automated tweets and their phones with switched phone calls including call guidelines.
Who is behind safeyourinternet.eu?
The campaign was organized by the organization Copyright for Creativity (C4C) and its secretariat N-Square. The C4C has 42 members (EFF, Edri, BEUC etc.) and, according to its own statements, is mainly financed by the Open Society Foundation (the foundation of George Soros) and the Computer & Communications Industry Organization. Members of this American industry association include Amazon, Cloudflare, Facebook, Mozilla, Google and Uber.
Who exactly was in charge?
To carry out the campaign, N-Square (a lobby company of the KDC Group, which also works for Google, among others) links to various campaign sites. Unfortunately, it is not always clear who is behind it, because only half of the partners and tool pages involved in the saveyourinternet campaign have an legal notice.
Not even saveyourinternet.eu itself has an about us, only further links.
The imprint obligation of the e-commerce directive is ignored.
Only on a second glance over a WhoIs-Lookup one learns that the page was registered by the C4C. The conglomerate C4C, KDC Group, N-Square has registered other websites that also play a role in this hack: fixcopyright.eu and voxscientia.eu. Neither of these organizations disclose who created them. Only through a Whois query can you trace it back to the KDC Group.
Who needs the EU data protection basic regulation?
The basic EU data protection regulation (GDPR), which has been in force since the end of May, naturally also applies to companies operating campaign sites in Europe.
In the case of the sites registered by the KDC Group and N-Square, however, this does not seem to matter to them.
Particularly critical at liberties.eu is the transmission of visitor data to the North American New Mode, the commercial subsidiary of Open Media, without reference in a data protection declaration. Platinum sponsors of Open Media include Google and Mozilla.
Only the Open Rights Group website has a data protection declaration in accordance with the basic regulation. All others are in breach of Article 13 of the GDPR.
A GDPR-compliant data protection declaration, in particular information on the processing of consumer data, is missing in all other cases. Responsible persons are not be named.
Arm in arm with supporters of piracy
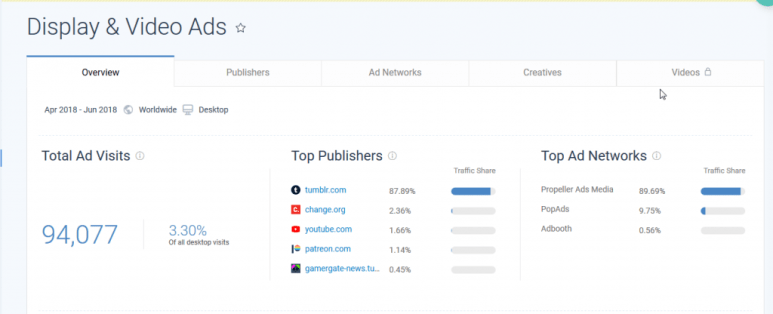
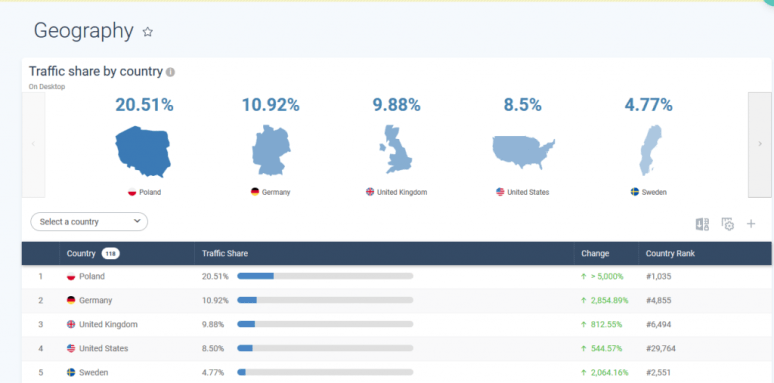
A further analysis of the traffic of Saveyourinternet.eu is very informative. Most of the visitors until the end of June came from Poland. This could have to do with the fact that there were Polish origin pages on which banners were placed. These banners were booked via the dubious English/Russian advertising network Propellerads. According to a study by the British company Incopro, Propellerads was the No. 2 ad network in 2015 that finances piracy sites through advertising. On illegal sites that violate copyrights commercially, Propellerads is an integral part of the advertising environment.
Illustration: Adtraffic to saveyourinternet.eu, 90% ads by Propellerads by Similarweb
Where are you from?
Visitors from the USA, who ranked 4th in the visitor hit list Saveyourinternet.eu, were also able to contact MEPs via the tools.
US blogger David Lowery describes in his blog Thetrichordist how he himself was able to reach EU deputies in the UK.
Illustration: Traffic share per territory by Similarweb
How much does a hack like this cost?
As several MEPs have told us, they have received between 50,000 and 70,000 emails.
If we assume that the Full Toolkit (Best Value) for 50,000 mails plus an additional package for 25,000 mails was ordered at New/Mode, the entire DDoS attack ADD “WOULD” cost only 549 US Dollar, i.e. about 470 Euro. That is only 0.60 euros per MEP.
Always assuming that several MEPs were bombarded with mails at the same time with one click.
Illustration: Price for the Full Toolkit (Best Value) at New/Mode
Conclusion
Ultimately, US companies from the Internet economy financed significant parts of a campaign in Europe to influence EU legislation.
What looked like grassrootes movement from the outside was in fact a classic form of astroturfing – designed to create the appearance of a popular movement.
Given the absence of any type of verification and the active marketing of this campaign outside of the EU, it remains entirely unclear the extent to which non-EU nationals and/or bots were involved in the generation of automated or semi-automated messages against articles 11 and 13 of the directive.
The campaign relied on dubious advertising marketers and many of the parties involved do not in the least meet minimum requirements for legal notice obligations and basic data protection regulations. There is massive violation of both.
This campaign was developed and executed precisely to create confusion about its sources, supporters and modalities, and to prevent a clear understanding of its true nature.
It is a matter of the greatest and immediate importance that the EU consider how to respond to such stealth attacks on the democratic institutions of the EU, and to ensure that such lobby-driven DDoS attacks will not endanger its ability to work fairly in support of the EU nationals and interests in the future. There is every reason to suspect that the same parties wil engage in similar, if not, identical tactics in the lead up to September vote on the directive, and therefor essential that steps be taken now to ensure against manipulation of our political processes by foreign and non-human actors.



You must be logged in to post a comment.