The Antitrust Division of the Department of Justice has announced the speakers for a series of public–but not too public please—workshops regarding the competition in licensing music public performance rights. Inevitably, this means a discussion of the ASCAP and BMI consent decrees. So why wouldn’t you want to be as inclusive as possible in a discussion about free market competition? Doesn’t the free market start with the free market of ideas?
Let’s be clear—as a general proposition, we despise these ancient consent decrees. There’s a very simple reason for that view: The consent decrees are like original sin visited upon the unborn.
We’re fully prepared to believe that some paper pusher pensioner at ASCAP overreached at some point in the distant past, just like paper pusher pensioners overreached with The MLC (another story, but a fine example of government run amok). People at ASCAP no doubt deserved punishment in 1941 (but the offenders no doubt kept their salaries and their pensions unlike the songwriters whose catalogs they mishandled). Instead of going after the individuals at ASCAP who broke the law, the government punished generations of songwriters, including those who were not even born yet The fundamental question is should the later generations of songwriters be denied due process because of something some nebbish did in the 1940s?
We think not. Yet what we have seen happen for generations is that all those who benefit from the administrative state created by the consent decrees want to keep it going. Like the cockroaches who survive nuclear holocaust, the destructive effects for songwriters matters little to these people as long as they get their salaries, bonuses and pensions unlike the songwriters they purport to represent. Because let’s remember—it wasn’t the songwriters who caused the problem. And if you want to fix the anticompetitive problem, just make it the personal responsibility of whichever bureaucrat messed up, not the organization and certainly not the songwriters. You won’t hear that idea from anyone on the DOJ’s panels.
In other words, whichever executive caused the problem in 1941 mishandled their responsibilities to the songwriters they were allowed to represent, and they are still doing it today. Nothing much has changed. And you know what else hasn’t changed? They are still collecting their salaries, bonuses and pensions. Songwriters still have the government’s boot on their throats with judges still trying to conjure up “market rates” where a free market doesn’t exist. The free market hasn’t existed for so long and technology has changed so much you could say a free market never has existed and all of this is a kafka-esque charade.
The point being—the Justice Department is on the right track in reviewing the consent decrees to absolve songwriters of the original sin. The push back DOJ is getting from the administrative state that has sprung up around the consent decrees should not be surprising. The transaction costs to songwriters are astronomical given the full employment for lawyers, accountants and experts required by rate setting under the consent decrees, all of whom no doubt make more from administering the consent decrees that over 50% (at least) of songwriters will ever make from royalties under the consent decree rate setting.
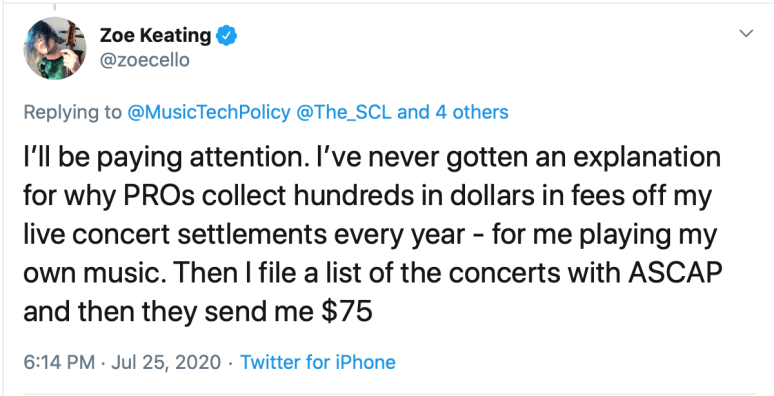
Case in point from Zoë Keating who will be watching the DOJ panels:
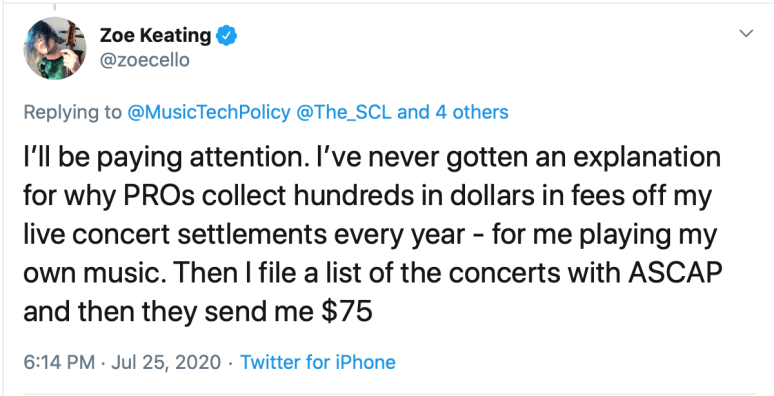
It’s for reasons like this that we look askance at the PRO’s braying about their collections and distributions. If they distribute $1 billion, we ask, how much did you cost the songwriters in hidden transaction costs for compliance (you know, like an unfunded mandate)? How much money did you miss in your porous collection system?
Another example: YouTube fails to pay songwriters for score or licensed music embedded in user-generated clips that the DMCA permits but does not provide guidance for (the related administrative state two aisles over in the “Safe Harbor” department). This is the DOJ’s consent decree at work with the equally pernicious DMCA safe harbor. Is anyone going to raise this issue? I doubt it. Why should they? DOJ has the government’s boot on the songwriters neck and the administrative state has their boot on the songwriter’s wallet.
Will these issues come up on the DOJ panels? Not from the line up of speakers that the lobbyists picked for the Antitrust Division’s public workshop. Those speakers will present a very tightly messaged order of battle to preserve the administrative state, their jobs, their bonuses and their pensions.
Another case in point is the movie theater exception. Unlike most of the rest of the major economies, movie theaters in the US do not pay songwriters and composers public performance royalties. This is the result of another ancient DOJ settlement that unfairly constrains income for composers and songwriters.
Let’s be very clear about movie theaters—what is about to happen due to the “COVID Consolidation” is that the streaming services are going to start buying theater chains. It’s already started with Netfix buying the Paris Theater in New York and the Egyptian Theater in Los Angeles, and analysts are anticipating Amazon would tie movie theater tickets to its Amazon Prime subscriptions, using content as yet another loss leader that drives down value of music and movies. Once that happens the antitrust consent decrees will be protecting the monopolies from songwriters. Does this seem completely ass-backwards to anyone else?
As the Society of Composers and Lyricists and the Songwriters Guild of America noted in their comments to DOJ:
[T]he principle “evidence” offered by the [National Association of Theater Owners in support of stiffing songwriters and composers] was, in fact, a forty-five year old case in which a mid-level employee of a third-party music licensing agent testified that she thought the forced combining of synchronization and movie theater performing rights was not an obstacle to her productivity. Citing CBS v. ASCAP, 400 F. Supp. 737, 760 (S.D.N.Y. 1975), the movie theater trade group stated:
In CBS, Albert Berman, managing director of the Harry Fox Agency, Inc. and Marion Mingle, the Fox employee who handled music rights, gave testimony describing the simple process they use to license both synchronization and performing rights for use in a theatrical motion picture—which can be completed roughly simultaneously most of the time. Mingle and her assistant were able to license “several hundred movies each year” this way.
Much has changed in the past half-century in regard to the licensing of musical works in films, but both SGA and SCL have little doubt one aspect of the process has not evolved in favor of music creators since the days of Ms. Mingle: that the Movie Theater Exemption has by default artificially relegated the value of US performing rights in motion pictures exhibited in US movie houses to at or near zero.
There is no good reason why the consent decrees ever needed to reach movie theaters as far as songwriters are concerned. We see only one reason why anyone wants that travesty to continue. As was widely reported at the time, streaming services—and theater owners—like Netflix got caught trying to jam buyouts of performance rights down the throats of composers:
At the end of October [2019], close to 90 composers and songwriters from around the world traveled to Budapest to discuss a contentious issue: streaming services’ efforts to upend how composers are compensated for their work.
Headlining the two-day International Council of Music Creators (CIAM) General Assembly was top Netflix music lawyer Carolyn Javier, who sought to defuse composers’ concerns over licensing contracts, known as buyouts, in which the streaming service pays them a one-time fee for all or most of the rights to their work, precluding them from receiving any backend royalties in the future. It has long been standard procedure for composers to be paid royalties for their compositions each time one is performed in a public setting: on the stage, at a bar, in a network TV or cable series, and now in audiovisual content streaming worldwide.
It’s obvious that if streaming services negotiate a buyout of performance rights for the music in their shows, it will apply across the board to the theaters they own. This gives them added protection just in case the movie theater exception should go away.
We believe this is exactly the plan that these Big Tech companies have in mind. Of course, if the DOJ had invited the CIAM—or its US affiliate Music Creators North America of which both the Society of Composers and Lyricists and the Songwriters Guild of America are members—then the Division might have had the opportunity to hear this side of the story directly from the songwriters and composers most directly affected by the shortcomings of the pensioners.
Motion picture and television composers are overrepresented in performance royalty earnings. By any estimates, a significant chunk of performance royalties are earned by these craftsmen and they are directly affected—almost exclusively—by the movie theater exception which the PRO pensioneers blithely give away. It is shocking that the DOJ has not included at least the Society of Composers and Lyricists in the not too public workshops, but it is not surprising—industry lobbyists have systematically excluded both the SCL and the Songwriters Guild of America from such hearings. Whenever we see the lineup of songwriter groups present at the not too public workshops, we know exactly how they came to be selected. It was not based on merit or representation.
You have to appreciate the irony of an anticompetitive suppression of voices by dominant forces being used to explore whether the consent decrees promote competition in the free market.
We can’t even have a free market of ideas to talk about the free market for songwriters.







You must be logged in to post a comment.